Synthetic transaction monitoring: what it is, how it works and why it matters
- azakaw

- 1 hour ago
- 13 min read
Synthetic transaction monitoring helps financial institutions detect hidden money laundering patterns that traditional rule-based AML systems often miss. Modern cybercriminals structure transactions to appear legitimate, keeping activity below predefined thresholds and spreading it across multiple accounts and entities to avoid detection.
To uncover these hidden behaviors, institutions need advanced monitoring approaches that analyze relationships, behavioral patterns, and transaction networks over time rather than relying solely on static rules.
In this guide, we explain how synthetic transaction monitoring works, the most common transaction typologies, and the technologies used to detect suspicious activity before it becomes a compliance failure.
Synthetic Transaction Monitoring: Key Takeaways |
|
|
|
|
|
What is synthetic transaction monitoring?
Synthetic transaction monitoring is the process of providing advanced tools to identify financial crimes that go beyond looking at individual transactions.
Unlike simple threshold-based systems, it identifies behavioral patterns. This process spans accounts, time, and related entities. Its goal is to identify and prevent financial crimes, including those that hide in plain sight.
Why is it difficult to track synthetic behaviour?
Tracking synthetic behavior in Anti-Money Laundering (AML), specifically regarding synthetic identity fraud, is difficult because these identities are constructed from a combination of real and fake data, allowing them to pass standard verification checks and mimic legitimate customer behavior.
Cyber-attackers engaged in activities creating synthetic behavior aim to evade rule-based transaction monitoring systems by:
ensuring no single suspicious activity crosses the threshold to trigger an alert.
keeping individual transaction amounts small:
operating through multiple bank accounts;
spacing out their activities to create an impression of normalcy.
Synthetic activity requires advanced capabilities to detect its underlying trends. What does 'synthetic' mean in the context of financial fraud control?

What is the difference between synthetic transaction monitoring and traditional monitoring?
Synthetic transaction monitoring and traditional transaction monitoring in Anti-Money Laundering (AML) differ primarily in their purpose and approach:
Synthetic monitoring acts as a proactive test of the system's ability to detect threats based on behavioral data.
Traditional monitoring is the active, rules-based surveillance of real customer transactions to find actual crime.
Traditional transaction monitoring systems ask: "Is this transaction suspicious?"
In contrast, advanced synthetic transaction monitoring systems inquire: "Does the customer's complete activity pattern, including all transactions and connections, indicate some kind of suspicious activity?"
Rule-based monitoring
Rule-based transaction monitoring involves applying predefined conditions to individual transactions.
Transaction monitoring based on rules involves setting rules to trigger alarms, such as:
If a transaction value exceeds a certain amount, then send an alert
If a customer sends funds to a high-risk country, then send an alert
If a customer receives 5 transactions on the same day, then send an alert
Rules offer clear, auditable, and understandable explanations for actions taken. However, they can only identify suspicious activities based on specific criteria mentioned within the rule itself.
Behaviour-based and network-based monitoring
Synthetic transaction monitoring employs behavioral data science techniques, including machine learning algorithms and network data visualization capabilities, to identify unusual patterns of activities that cannot be detected by any individual rule.

The Best Transaction Monitoring Tool
Stay ahead of risks with azakaw! It's an intelligent and AI-powered AML Transaction Monitoring System that detects, prevents, and resolves suspicious activities in real-time.
Why traditional systems miss synthetic activity
Since rule-based systems monitor transactions in isolation, they cannot identify money laundering activities.
All transactions in a money laundering scheme appear normal and do not trigger any of the rules, as they are designed to evade detection using this limitation.
Money laundering schemes create financial crime. This crime cannot be detected until we look for relations between several transactions. These transactions are spread across various accounts, times, or entities.
Good monitoring systems can identify such schemes.

What are synthetic transactions and synthetic activity?
The word "synthetic" here doesn't mean fake in isolation. It means constructed, deliberately assembled to look normal while serving a criminal purpose.
Understanding what this looks like in practice matters for building detection that actually works.
What do synthetic transactions mean?
A synthetic transaction appears genuine on its own but is part of a complex web of criminal activity. It can be a conventional bank transfer, a small transaction, or a routine credit to an account.
What characterizes it as synthetic is its role in a broader scheme. It facilitates money laundering through several routes to obscure the source or destination of funds.

Synthetic identities vs synthetic transaction behavior
While they are related issues, identity synthesis and transaction pattern analysis represent two types of challenges.
Synthetic identities are based on fake or interpolated personal data. This creates a bogus customer entity, posing a challenge in detecting Financial Crimes and Know Your Customer (KYC) breaches.
Synthetic transaction behavior refers to normal/synthetic account patterns of transactions in a coordinated manner, with the intent to move proceeds of crimes.
In cases involving genuine or regular customers acting as "money mules" who assist others in financial fraud, there may be no attempt to create fraudulent identities.
Read also: What is KYC verification?

Why is synthetic transaction monitoring important in AML compliance?
Synthetic transaction monitoring is important to prevent more advanced money laundering schemes and financial crime methods that a rule-based system can't.
Rule-based systems were designed to find crimes that follow specific patterns or signs of suspicious behavior. However, there is a significant gap between what existing systems can detect and the sophisticated methods used by criminals to circumvent those very rules.
Role in detecting complex money laundering schemes
All money laundering schemes via mule networks, layering techniques, or trade-based schemes involve a synthetic transaction flow.
Rather than making a single large suspicious transaction, criminals create a complex web of transactions across numerous accounts, parties, and timeframes.
Good-quality synthetic transaction monitoring can identify the underlying network and transaction pattern rather than focusing solely on individual suspicious transactions that may fall below certain thresholds.

Supporting the risk-based approach
As per FATF's risk-based approach, financial institutions need to apply effective risk management measures commensurate with the level of risk they pose. Good synthetic transaction monitoring tools enable effective, risk-based decisions.
These are backed by data-driven behavioral customer risk profiles based on transaction history. This contrasts with assigning a fixed risk score based on onboarding information.

A Single Source of Truth
Drive business growth and operational efficiency with our fully customisable solution. Empower your risk-based approach with a no-code customisation software.
TIP: Read everything you need about AML compliance risk management
Increasing complexity of financial crimes
Financial crimes are constantly evolving. The UN Office on Drugs and Crime (UNODC) reports that money laundering schemes are becoming increasingly complex. They involve multiple layers, international connections, and increased use of technology to conceal them.
To keep ahead of such crimes, the detection systems must improve and go beyond regulatory requirements.
In our experience, synthetic transaction monitoring is a key component of these efforts to stay ahead.
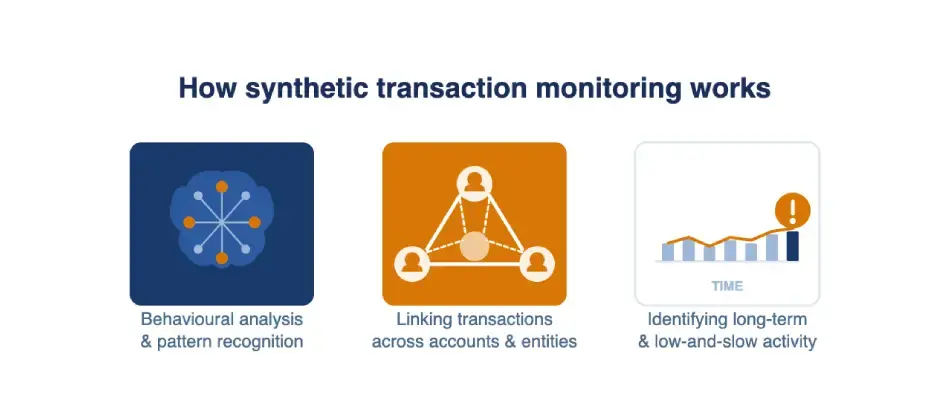
How synthetic transaction monitoring works
The method of working of the synthetic transaction monitoring system is quite distinct from conventional rule-based systems. Key features of synthetic transaction monitoring include:
Behavioral analysis & pattern recognition
Based on historical transaction data, Synthetic Transaction Monitoring creates a behavioral baseline for each customer. It incorporates personal details like:
transaction values
time frames
counterparts
communication channels
transaction frequency
etc
Advanced machine learning algorithms detect any deviation from the established behavioral baseline.
These deviations can indicate unusual transactions possibly linked to financial crimes. This is an example of Anomaly Detection rather than mere rule-based transaction monitoring.
Linking transactions across customers, accounts, and entities
Graph analytics and entity resolution allow synthetic transaction monitoring tools to create connections. These connections link customer accounts, transactions, and data. These connections are not apparent from regular data systems.
Consider two bank accounts involved in transaction flows at different times with a common counterparty. When viewed as part of a network, these may suggest a money mule operation. This is true despite each account being clean on its own.

End-to-End Compliance Solution
Are you looking for an AML powerhouse? azakaw unifies your data, leveraging AI and Machine Learning to map complex entity links and expose hidden fraud. Centralize your intelligence, detect schemes instantly, and scale with total clarity.
Identifying long-term and low-and-slow activity
Certain types of fraud can continue for months or even years with minimal activity. The goal is to evade detection.
Conventional monitoring tools fail to identify these attempts. This is because their historical data review capability, or lookback window, is limited. Any suspicious transactions are isolated and do not significantly contribute to the total value.
Synthetic transaction tracking tools help monitor large datasets over extended periods. This allows for the identification of patterns in escalating transaction values. Such transactions, which do not trigger any individual transaction-based rules, will be caught by this approach.

What are the common synthetic transaction typologies?
Synthetic transaction typologies are transaction patterns designed to disguise illicit financial activity by mimicking legitimate customer behavior. These typologies are commonly associated with account laundering, mule activity, fraud rings, sanctions evasion, and synthetic identity abuse.
Account layering and mule networks
A 'mule' account refers to a customer account, sometimes held by an innocent person who has been duped or deceived, used to receive and transfer illicit funds.
In a money mule network, money flows through multiple bank accounts in a series, with each transaction appearing as normal.
Transaction fragmentation and value cycling
Transaction fragmentation, also known as layering or smurfing, involves dividing large sums of money into smaller transactions. This is carried out through multiple accounts or time periods to avoid breaching reporting limits.
Value cycling involves moving funds in circles of accounts to create the appearance of significant transaction volumes and conceal the source of the funds.
Both types of transactions need information across multiple bank accounts spanning over extended periods to detect them.

Stay Ahead of Risks
Learn how azakaw streamlines compliance from identity and business verification to corporate compliance and AML transaction monitoring, reducing costs and complexity so you can scale with confidence.
Dormant account activation patterns
An account dormant for several months suddenly becomes active. It performs transactions along with other dormant accounts on the same day, involving common beneficiaries.
Cross-account and cross-entity behavior
Related bank accounts (held by connected individuals or entities) engage in offsetting financial transactions without any obvious linkages.
Graph analytics tools help identify these relationships based on attributes like IP address, device, phone number, beneficiary, and timing.
Each account appears clean on its own, making these tools invaluable! Connections among them reveal intricate money laundering schemes!

Key red flags of synthetic transaction activity
These are the signals your monitoring system and your analysts should be trained to recognise.
Anomalous transaction times and sequences
Transactions occurring in regular timed clusters or following strict patterns throughout multiple accounts raise suspicions. Good customers' transactions are always varied and unpredictable. Synchronized fake transactions show a regular pattern.
For example, this could be a transfer every week or payments sent out in a similar order from various bank accounts.
Abnormal transaction timing and sequencing
Multiple transactions clustering together in precise timing patterns suggest possible concerns. They might also appear in rigid sequential orders on multiple accounts.
Legitimate customers make transactions with varying levels of unpredictability.
Well-coordinated synthetic activities show regular patterns. This may include transfers made at the same time every week or payment orders placed in similar sequences in various accounts.
Repetitive low-value transactions across accounts
Frequent low-value transactions involving multiple accounts add up to substantial amounts. This is especially indicative of synthetic activities when the receiving account forwards the money onward.
Individual transactions may be too small to trigger alerts based on defined risk parameters. However, the aggregate flow that spans multiple accounts over time reveals concerns about Synthetic Transactions.
Hidden relationships between customers and entities
Common device IDs, overlapping IP addresses, consistent phone numbers, and identical email domains on accounts with no apparent connection may suggest suspicious synthetic activities. So, these attributes warrant further investigation.
Identifying common attributes among these related accounts, i.e., Entity Resolution, helps uncover any links between seemingly unrelated entities. This process is crucial for a comprehensive view. This needs to be done before they can be exploited further.

Who needs synthetic transaction monitoring?
All financial institutions dealing with significant transaction volumes need to assess their systems. This is especially true if they are exposed to organized financial crimes.
They must identify if rule-based systems alone can effectively manage financial crimes.
Banks and financial institutions, especially those with high volumes of retail or cross-border transactions, are most vulnerable to money mule schemes and layering crimes. Consequently, they face greater risks. They also have the required infrastructure to enable effective synthetic transaction monitoring.
Fintechs and payment service providers (PSPs) handle huge volumes of transactions. They often have limited resources for their compliance teams. Effective automated synthetic transaction monitoring capabilities are necessary to ensure adequate coverage without increasing unnecessary manpower.
Cryptocurrency platforms and VASPs are at risk of new types of layering scams. These scams are often based on blockchain technology and cross-chain value cycling, which regular TM systems might not identify. Financial institutions dealing in cryptocurrencies expect sophisticated synthetic transaction monitoring tools equipped with on-chain data analysis capabilities.

Secure Blockchain & Crypto Compliance
Address the distinct compliance needs of digital assets with AI-powered tools designed to simplify regulatory challenges and drive innovation in blockchain technology.
Read also:
Penalties and business losses caused by weak transaction monitoring
Regulators have made clear that inadequate transaction monitoring is a serious, enforceable failure. It is not simply a technical gap. The consequences are significant.
Regulatory fines and enforcement actions
Financial Conduct Authority (FCA), FinCEN, and other global regulatory bodies have imposed large-scale fines for inadequate transaction monitoring. These actions highlight the severity of the issue.
Deutsche Bank, HSBC, and NatWest are examples of banks that have been dealt major blows. This occurred under various financial crime compliance regulations due to their inadequate transaction monitoring systems.
The Financial Conduct Authority has clearly stated that financial institutions must ensure effective transaction monitoring systems. These systems must be capable of detecting sophisticated financial crimes, which poses a challenge for rule-based systems.
Supervisory findings and damage to reputation
Regular thematic reviews and onsite inspections reveal TM gaps as significant issues of concern.
Even if a regulatory body identifies shortcomings in your current Transaction Monitoring system, bridging these gaps is costly and disruptive. It involves upgrading capabilities, reviewing models, training analysts, and external expert certification.
Damage to Goodwill resulting from any public action taken by a regulatory body is hard to quantify, but can continue to have financial implications for years after the financial penalty has been paid.

The Best Transaction Monitoring Tool
Stay ahead of risks with azakaw! It's an intelligent and AI-powered AML Transaction Monitoring System that detects, prevents, and resolves suspicious activities in real-time.
Increased exposure to financial crimes and compliance costs
Poor surveillance measures increase the vulnerability of your institution to being used as a channel for money laundering.
Beyond the risk of non-compliance, increased vulnerability to financial crimes leads to fraud losses and restrictions on correspondent banking services. It also results in increasing compliance costs due to escalating loopholes.
Investing in adequate surveillance measures is invariably cost-effective compared to rectifying a deficiency in surveillance measures after it has occurred.
What are Synthetic transaction monitoring tools?
Knowing what these tools can do allows Compliance Teams to create effective strategies for investing in effective anti-money laundering technologies.
Core capabilities of synthetic monitoring tools
Effective synthetic transaction monitoring tools offer capabilities that go beyond existing Rule-Based systems:
Behavioural Baseline modelling: creating detailed profiles of individual and group behaviour based on available transaction information, which can be updated in real-time as new data flows in
Graph and Network Analytics: identifying complex networks involving accounts, entities, and transactions to uncover suspicious schemes
Entity Resolution: providing visibility of customer information scattered across multiple internal and external data sources through attributes to reveal latent connections
Extended Lookback Analysis: enabling identification of suspicious patterns over extended periods of time, such as months, rather than mere days

AI-Powered AML Compliance Tool
azakaw powers advanced AML through Behavioural Modelling, Graph Analytics, and Entity Resolution. We automate synthetic monitoring and complex detection, reducing risk so you can scale with confidence.
Machine learning and behavioural models
The Machine Learning algorithms used in Synthetic Transaction Monitoring tools learn from historical transaction data. They identify signs of Financial Crimes without needing explicit rules.
Supervised machine learning algorithms are trained on known data points of financial crimes.
Unsupervised ones can identify anomalies without any previous knowledge of financial crimes. Both contribute to creating Suspicious Activity Reports (SARs) that supplement the alerts generated by the rule-based system instead of replacing it.
Challenges in implementation
Synthetic Transaction Monitoring Solutions require high-quality and integrated data to function effectively. Unless your customer, account, and transaction details are kept centralized and easily accessible (without being siloed), network analysis cannot pick out the meaningful connections needed to identify suspicious activities.
Another challenge is Model Explainability: Regulators need banks to be able to provide reasons as to why a particular customer has been identified by a model.
'Black Box' techniques do not provide enough detail to meet these demands.
Managing False Positives is important, too. Though advanced models reduce instances of false positives, necessary steps like regular alert tuning and effective workflows for Analysts remain crucial!

Frequently Asked Questions
Is synthetic transaction monitoring mandatory?
While no specific regulation mentions "synthetic transaction monitoring," the Financial Conduct Authority (FCA) and Financial Crimes Enforcement Network (FinCEN) require all businesses to have systems capable of identifying relevant financial crimes. If these include "coordinated" or "network-based" scams, rule-based systems alone may not provide adequate anti-money laundering capabilities.
How is synthetic activity different from fraud?
Fraud involves deceiving to gain financial benefits, such as identity theft, unauthorized transactions, or account takeovers.
Synthetic transaction activities primarily relate to money laundering, attempts to launder dirty money through legitimate financial channels, creating uncertainty about its source. Although Synthetically created identities are used in both fraud and Money laundering, strategies to deal with them differ.
Can synthetic transaction monitoring be automated?
Yes, it can. Automated transaction monitoring enables financial institutions to embrace technologies like Machine Learning, Graph Analysis, and Behavioral Detection. These provide 24/7 operational efficiency, requiring minimal human intervention.
Human experts take care of investigating alerts generated by Machine Learning algorithms. Completely delegating tasks to machines leads to risks of errors of law as well as technological capabilities.
How do regulators view synthetic monitoring models?
Regulators support advanced analytics in transaction monitoring systems. However, they require firms to set up and manage models, explain their workings, check for data biases, and provide easily understandable information on output results.
The Financial Conduct Authority (FCA) and Financial Crimes Enforcement Network (FinCEN) have guided the management of model risks applicable to Anti-Money Laundering (AML) systems.
Conclusion
Rules-based transaction monitoring is suited to a simple financial crimes environment. But since financial fraudsters have already developed ways to beat this approach, we have Synthetic Transaction Monitoring.
Financial criminal behavior, including complex money laundering networks, concealed transactions, and circular asset flow, often goes undetected. These activities do not appear as individual suspicious transaction reports.
Patterns of synthetic fraud emerge from relationships between transactions, accounts, and entities. These complex interactions occur over time periods that standard rules and warnings typically overlook.
Identifying these patterns using advanced monitoring provides banks with a significant opportunity. Consequently, they can lead the fight against financial crimes. Effective risk and analytical techniques are now demanded from all financial institutions worldwide.
If you're assessing your current transaction monitoring program or evaluating tools that go beyond rule-based detection, Azakaw works with banks, fintechs, and compliance teams to design monitoring frameworks — including synthetic and behavioural detection — that match the actual sophistication of the risks you face.

The Most Powerful Monitoring Tool
Are you looking for an AI-powered compliance solution? Discover how azakaw uses machine learning to improve AML detection, reduce risk, and adapt to evolving threats.
Related content:






